A search of the term VoIP Phone Vulnerabilities results in a torrent of articles discussing network hacking and how to protect networks from outside intruders. VoIP data protection is a legitimate security concern I.T. departments must address. However, it is too often overlooked that VoIP phones are still just phones that transmit conversations from one point to another using cable. In some cases, many of the same cables are used for the VoIP phone as the POTS phone that preceded them. Continue reading “Testing VoIP Phone For Non-VoIP Vulnerabilities”
Tag: TALAN
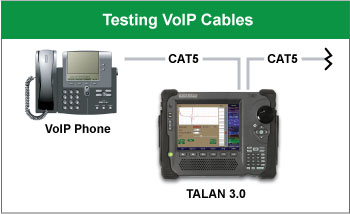
A. Physical Line Test
The LINE and PHONE ports on the TALAN input panel are used when testing conductivity of analog, digital and VoIP cable conductors. This is where DMM, NLJD, FDR and other line tests can check for conductive anomalies on VoIP cables.
The TALAN is capable of detecting VoIP packets on VoIP phone systems using the 10/100 Mbps rate. The TALAN VoIP Test Adapter will force some Gigabit VoIP systems to auto-negotiate to the 10/100 Mbps rate. However, some VoIP network systems may not be fully compatible with the VoIP Test Adapter, or have been set up not to auto negotiate down. Below are compatibility issues that may be encountered and also solutions:
Continue reading “Testing Gigabit VoIP Systems with TALAN 3.0”
Research Electronics International is pleased to announce the TALAN 3.0 Telephone and Line Analyzer with enhanced VoIP analysis and new earth/shield/ground testing. The portable TALAN 3.0 analyzes digital, analog, and VoIP phone systems and wiring for faults, anomalies, and security risks using a suite of telephone tests including an automatic switching matrix.
What’s New in TALAN 3.0:
- VoIP traffic analysis on phones, networks
- Patent-pending FFT algorithm for visual display of VoIP traffic
- Earth/Ground testing for modified connections to extraneous wiring
- Advanced input panel to accept and test shielded ethernet cables
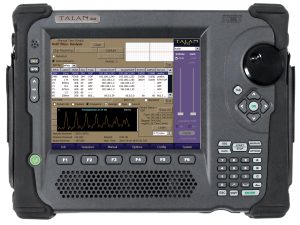 The TALAN Telephone and Line Analyzer provides many automated tests in a single product to detect and locate illicit surveillance devices (wiretaps and electronic surveillance/eavesdropping products) on telephones, communication and other types of wiring, and is the only product of its kind in existence.
The TALAN Telephone and Line Analyzer provides many automated tests in a single product to detect and locate illicit surveillance devices (wiretaps and electronic surveillance/eavesdropping products) on telephones, communication and other types of wiring, and is the only product of its kind in existence.
Developing technologies and growing acceptance of VoIP telephones have also brought increased opportunity for exploitation. A VoIP phone can be programmed to pass VoIP data, even when it appears inactive; for example, a VoIP phone can be compromised by someone with network access (e.g. IT personnel, hacker) and the ability to turn the microphone on and off, effectively collecting and transmitting room audio undetected.
Continue reading “New TALAN 3.0 Offers Advanced VoIP and Shielded/Earth/Ground Cable Tests”

Research Electronics International recently released a software update for the TALAN Telephone and Line Analyzer, version 2.04. The update can be downloaded from the website and includes installation instructions with the update files. Upcoming firmware updates will include enhancements to VoIP features. Version 2.04 improves several key TALAN functions.
The majority of REI products are packed in customized hard shell composite Mil-Standard cases to provide the most durable protection available. The majority of customers desire packaging that can endure rugged handling for the life of the product.
The previous installment in this series discussed analog telephone threats commonly overlooked in business environments. In this second installment, focus is directed to digital and VoIP phone system threats. While threats like packet capture of VoIP traffic may be obvious, we are going to highlight some less-complicated threats that are easily addressed, providing a large security benefit.
Continue reading “Is Telecom Security Still A Concern? – Part Two”
In this two part series we will be answering this question, “With the emergence of RF and wireless threats, is telecom security still a concern?” The first part of this series will focus on common telephone threats with part two addressing digital and VoIP threats.
Continue reading “Is Telecom Security Still A Concern? – Part One”